The world has changed. Gone are the days of relying on physical pieces of paper to transport information. All these communications and countless other processes have been moved to cyberspace, and this transition has enabled amazing improvements in productivity and efficiency. However, by relying so heavily on the internet, entire nations have created new attack vectors for malicious outsiders.
Threats to national security can no longer be found on a map. Hackers come from anywhere at any time, a lesson the U.S. recently learned from the distributed denial-of-service attack that befell internet performance management firm Dyn. This particular incident – which caused downtime for sites as large as Twitter and Netflix – highlights just how unprepared America is for cyberattacks, and serves as a reminder for organizations everywhere to beef up corporate cyber security.
Dyn DDoS cyberattack underscores a big flaw
Before delving into the ramifications of this event, let’s first take a look at what actually happened. In the early hours of Oct. 21, 2016, Dyn was hit by a massive DDoS attack. This specific hacking technique is where a cybercriminal sends an enormous amount of traffic toward a network in the hopes of crashing it. In this case, Dyn’s servers were unable to handle the loads of data being thrown at them and crashed.
This was significant because these machines weren’t just regular servers: They were part of Dyn’s domain name system. DNS infrastructures basically allow users to match up the domain names they type in with the IP addresses of the websites they want to visit. In a sense, these systems act as a middle man to get you where you’re trying to go on the internet. Without this DNS infrastructure working properly, users in the eastern U.S. had a lot of trouble connecting to big sites.
“This wasn’t a single attack.”
On top of that, this wasn’t a single attack. Dyn put out a statement saying that there were technically three DDoS waves, although only the first two seem to have affected customers. When the smoke cleared and Dyn had some time to analyze the incident, the company found that “10s of millions of IP addresses” were involved in the plot, which suggests a botnet was used (more on that below).
Who’s to blame?
As it is with most cyberattacks, figuring out exactly who was behind this incident is going to take a lot of time and research. A hacking collective that calls itself New World Hackers has since claimed responsibility for the 2016 Dyn cyberattack, according to Politico’s Tony Romm, but there is currently no real evidence to support this . A lot of groups like this one will jump at the chance to say they were behind such a major event, as it gives them prestige and gets their names in the news.
What is known is that devices considered part of the Internet of Things played a role in this incident. A hacker that goes by the name “Anna_Senpai” recently released the source code for a malware variant that allows criminals to gain control of large swaths of IoT gadgets and create botnets out of them, according to security firm Flashpoint. This same malware, which is called Mirai, was used in the Dyn cyber-attack.
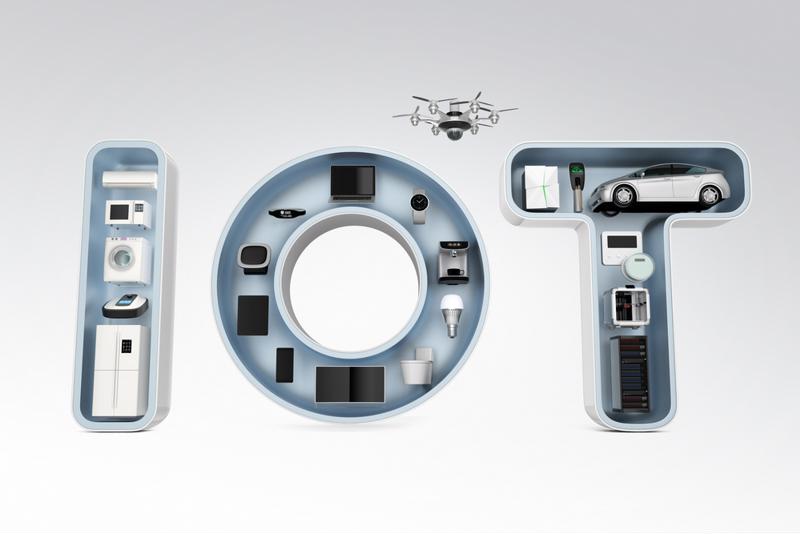 The Internet of Things can allow hackers to create giant botnets.
The Internet of Things can allow hackers to create giant botnets.Again, there’s no hard evidence here, but this could suggest that the 2016 Dyn DDoS cyberattack came from an individual or a small group, rather than a large collective or nation-state. In fact, security expert Brian Krebs cited a “trusted source” that had observed online conversations between nefarious individuals discussing a cyberattack levied at Dyn.
If this is true, it would mean that all it takes to bring the customer-facing operations of major companies to their knees is to leverage some open source malware that anyone with the right knowledge could find on the dark web. What’s more, if individual hackers do turn out to be responsible, what kind of power do well-funded nations hold?
What can companies do to mitigate the risks?
Although these kinds of threats obviously need to be handled by the American government itself along with network service providers such as Dyn, the average organization can still take steps to prevent business interruptions due to a DDoS attack. In terms of this recent incident, Dan York of Internet Society has recommended working with multiple DNS providers. This allows you to fall back on another partner, should a primary vendor not be able to handle something like the Dyn DDoS attack.
However, another great way to alleviate the strain of cybersecurity issues and business security risks is to utilize multiple forms of communication. This is why Fax over IP is such a great way to transfer important information. Not only is FoIP an extremely secure fax alternative in-transit, but FaxCore’s services work different than other digital messaging platforms and are often available when email isn’t.
Enhance enterprise communication, collaboration and compliance efforts with a proven FoIP solution from FaxCore. Contact FaxCore today to learn more about their ‘Partly-Cloudy’ fax solutions.